I’m still cleaning up after Heartbleed – a little bug that essentially rendered a lot of encrypted communications completely useless from March 2012 to now. Plus they get bonus points for giving the bug a really cool, scary name. Plus like a totally awesome logo. That’s the best marketing for a security vulnerability I’ve ever seen.
I remember a long time ago, back before email used the @ sign, when mail was bounced from machine to machine to machine, and you needed to know not only who you wanted to talk to, but what machine they were on, and what machines talked to their machines. I was uunet!sobeco!paxmtl!sean back then, cause most everyone knew how to get to the uunet machine.
That’s when I remember being told, and I forget by who, about email security.
“Think of email as if you’re sending a postcard”.
Ponder that for a bit. It implies that anyone along the way can read your email. Have no expectation of security.
If you’re working on confidential stuff, you can ask me to sign an NDA. Or do what I do: Keep your mouth shut. If it’s a real secret, like an awesome patent application, keep your mouth shut until you file, then talk.
I was also an admin at the time of the first, huge, computer security episode in 1988 – The Morris Worm. We weren’t affected since we were running a relatively obscure version of Unix that was immune to the worm. Robert Morris is now with Y-Combinator, and doing more cool things. The case was resolved amicably in large part because his father, also Robert Morris was a cryptographer as well as the Chief Scientist at the NSA’s National Computer Security Center.
He has some great security rules:
- The three golden rules to ensure computer security are: do not own a computer; do not power it on; and do not use it.
- Never underestimate the attention, risk, money and time that an opponent will put into reading traffic.
Funny about that Heartbleed bug. A little bad code in an open source product OpenSSL 1.0.1 through 1.0.1f (inclusive) are vulnerable. The thing about Open Source is that anyone can go look at that code, use it, and change it. You, me, the NSA. That’s a level playing field. No backdoors, nothing funky.
The availability of code for public inspection is supposed to increase its security (many eyes). In this case it didn’t.
In the aftermath of the Heartbleed bug, Bloomberg published an article that the NSA may have had access to this bug, and may have been using it to collect information for years.
Pssst…. everyone… THAT’S THEIR JOB. If the US has a spy agency that couldn’t and didn’t do that they’d be a bunch of idiots.
The real problem is that now that the exploit is out in the open, with source code to match, every kid from here to Kiev is going to be pounding on unsecured servers. That’s really gonna suck.
So boys and girls, do change your passwords.
But what about the massive collection of information by the NSA? Isn’t it terrible?
No, not really. Not if you consider everything you put of there as being on a postcard.
The collection of information in itself isn’t really a problem. The tricky part is what that information gets used for, by whom, and under what circumstances.
J. Edgar Hoover had private files on lots of people full of embarrassing secrets – and he used them. So it’s not the data that’s important – it’s 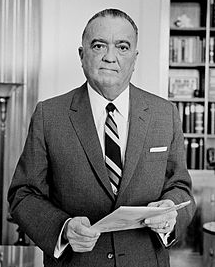 having data which when placed in context, becomes leverage.
having data which when placed in context, becomes leverage.
“While there is ample evidence that Hoover used the information in his files for blackmail, there was usually no need for it. Simply the perception that he had such information was enough to keep politicians in line.”
Here’s a secret. Google and Facebook know more about all of us than the NSA ever will. And while Google has generally been pretty good with privacy, Facebook really hasn’t… and they don’t intend to be either.
 The only difference is they tell you right in the terms of service and permissions you have to give their app what they want. In short their app wants permission to:
The only difference is they tell you right in the terms of service and permissions you have to give their app what they want. In short their app wants permission to:
- Read your text messages (SMS or MMS)
- Download files without notification
- Read/write your contacts
- Add or modify calendar events and send email to guests without owners’ knowledge
- Read calendar events plus confidential information
Noodle on that for a while. Sounds like Facebook can do whatever the hell they want with your phone and data, and can do it on your behalf, without telling you. And use it for marketing. Or whatever. With your permission of course, because nobody reads Terms of Service anyhow.
We’re giving away more privacy and security than ever before. That’s the problem.
1 comment for “Privacy and Security on the Internet circa 2014”